Secure IT Infrastructure 570010341 Online

A secure IT infrastructure is critical for organizations operating online. It serves as the foundation for digital operations while safeguarding sensitive information from emerging cyber threats. By incorporating risk management strategies and security protocols, organizations can effectively mitigate vulnerabilities. However, the complexities of modern cyber risks necessitate a deeper understanding of best practices and technologies. As threats evolve, organizations must continuously adapt their security measures to maintain resilience. What effective strategies can be implemented to stay ahead?
Understanding the Importance of a Secure IT Infrastructure
As organizations increasingly rely on digital systems to conduct operations, the significance of a secure IT infrastructure becomes paramount.
Effective risk management strategies must be implemented to mitigate potential threats.
Heightened cybersecurity awareness among employees is essential, fostering a culture of vigilance.
This proactive approach not only safeguards sensitive information but also enhances organizational resilience in the face of evolving cyber threats.
Essential Components of an Online IT Security Strategy
A robust online IT security strategy encompasses several critical components that collectively fortify an organization’s digital environment.
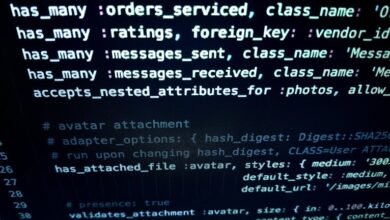
Key elements include implementing data encryption to protect sensitive information and establishing stringent security protocols to govern access and usage.
These components work synergistically, ensuring that vulnerabilities are minimized, and the integrity of digital assets is maintained.
Ultimately, this empowers organizations to operate securely and efficiently in the digital landscape.
Best Practices for Protecting Your Digital Assets
Protection of digital assets necessitates a comprehensive approach that integrates various best practices tailored to an organization’s unique needs.
Effective data encryption safeguards sensitive information, rendering it unreadable to unauthorized users.
Additionally, implementing robust access control mechanisms ensures that only authorized personnel can access critical resources, thus minimizing the risk of data breaches and enhancing overall security posture within the organization.
Tools and Technologies to Enhance IT Security Online
Implementing effective strategies for safeguarding digital assets lays the groundwork for exploring the tools and technologies that can further enhance IT security online.
Advanced cloud security solutions provide robust protection against unauthorized access, while sophisticated threat detection systems utilize machine learning algorithms to identify and mitigate potential vulnerabilities.
Together, these technologies empower organizations to maintain a resilient IT infrastructure, ensuring freedom from cyber threats.
Conclusion
In conclusion, a secure IT infrastructure is not merely an operational necessity but a strategic imperative for organizations in the digital age. While some may argue that the costs of implementing robust security measures are prohibitive, the long-term benefits—such as safeguarding sensitive data, maintaining customer trust, and ensuring business continuity—far outweigh these initial investments. By prioritizing security through comprehensive strategies and advanced technologies, organizations can effectively mitigate risks and thrive in an increasingly complex cyber landscape.